We discussed exchanges and what role they pay in the cryptocurrency investment ecosystem in last week’s Deciphering Cryptocurrency. Next up is wallets and security.
You and you alone are responsible for your cryptocurrencies.
Their security is only your concern.
That axiom is going to underpin everything written here today.
Private and public keys
A private key is a secret number the lets you access and spend your cryptocurrency. They’re related to all cryptocurrency addresses generated for the wallet and every wallet contains at least one. Private keys can be kept in digital form, but can also be written down.
The end user rarely sees the key, but instead is given a seed phrase that encodes the same information. The private key is private. Protect it with your life. It authorizes you to carry out any other transaction from your account.

A public key can be shared with people on the network, unlike a private key. It’s used to allow a user to receive cryptocurrencies into their account. The public key and the private key are both integral to ensure the security of the crypto economy.
The moment you make your first cryptocurrency transaction, a pair of public and private keys will come into existence. These correspond to a long string of alphanumeric characters that keep a user’s holdings secure in the digital ecosystem. An algorithm using math too fancy to get into here is applied to the private key to generate the public key, and both keys are stored in the wallet.
Wallets
A cryptocurrency wallet is a digital wallet that you can use to store, send and receive various cryptocurrencies. It’s important to note that the wallet doesn’t exactly “store” your money as a real-world wallet does. Instead, it saves your public and private keys which in turn helps you send and receive money.
They come in two different basic types: hot and cold wallets.
But there is a lot of variation within those two basic types, and it’s important to pick the right wallet, depending on what it is you’re looking to do with your crypto. The choices you make for a long position on Bitcoin will be different if you’re looking to make high-frequency cryptocurrency trades on an exchange.
Cold Wallets
A cold wallet is any type of crypto-storage device that’s not connected to the internet. These commonly come in two different formats: paper wallets and hardware wallets.
Paper Wallets
Some people go so far as to buy the cheap $300 laptop regularly pawned off on students every September by Best Buy and devote it entirely to their crypto-enterprises. They outfit the laptop with the best firewall money can buy, and get themselves an old school printer, which they dutifully hook up using a cord to avoid compromising their security by using wifi. Then they print off their private keys and stuff them away in a safe.
The pros for this one are pretty simple:
Your investment is offline and therefore not at risk of being stolen by hackers. It’s still at risk of being stolen via home invasion, but that’s why you’ll need a safe (or a safe-deposit box) big enough that nobody can carry out.
The cons on this method are somewhat complex, and they stem around what kind of hardware you’re using to print your keys off. In this case low-tech is best. Do this at home using your secondary computer, which you store offline with no connection to the internet, and directly connect to a printer that you’ve dedicated to cryptocurrency.
Print your keys off and stuff them in a wallet, and then clear your cache and cookies, disconnect your printer and computer and stash them in the same safe as your keys.
If this sounds like a lot, then keep in mind that lots of printers have an internal hard drive where the paper wallet will be saved. The private key will be available to anyone with enough technical skill to find and read the file. Shared printers, such as those in schools, officers and internet cafes, are similarly verboten, because they’re monitored and usually logged.
Wifi is also open to hacking, because even the most moderately skilled hackers are usually technically inclined enough to be able to steal your private keys.
No matter what type of wallet you choose, your best weapon to keep your cryptocurrency safe is your mouth. Don’t open it. Don’t tell anyone about your cryptocurrency adventures, and nobody will think to ransack your house looking for the safe that holds your keys.
Hardware wallets
Hardware wallets are devices designed to safeguard your cryptocurrency.
One of the benefits of a hardware wallet is that a flooded house or someone making off with the safe that holds your cold stored bitcoin keys can mean disaster, but hardware wallets can be restored. That also means you should back up your hardware wallet, and keep the restoration details safe.
Both of the below devices come with two-factor identification, and plenty of other safety related goodies, and they’re both from reputable companies with good track records.
The USB stick style Nano Ledger series is one of the most common types of hard ware wallet.

The most paranoid bitcoin aficionados get their tinfoil hats on about third-party hardware wallets, offering up conspiracy nuggets like ‘you’re trusting that the company who made your wallet hasn’t logged all the private keys with a plan to raid wallets in the future.’
The nutcase factor on that one is pretty high, but it does extend to a point about buying one of these secondhand—namely: don’t. Because the above scenario could become a reality.
Another common wallet is the Trezor One.
Light, compact and good for travel.
It’s fine to take your Trezor with you on the airplane. Like all modern electronics, the X-Rays won’t hurt it, and it supports more than 500 coins.
But even with these wallets, you’re going to want to watch out for the fakes and the knock-offs.
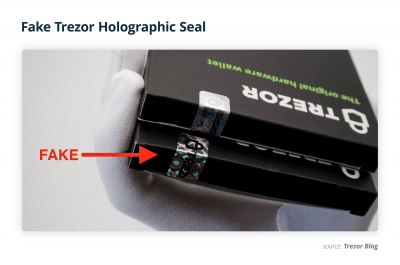
[PSA] In recent weeks we have discovered a non-genuine Trezor One devices which try to imitate the original to the bone.
For more information on how to spot a fake Trezor One device, please read our latest blog post here: https://t.co/tpe21iTVXm
— Trezor (@Trezor) November 19, 2018
Manufacturer development team SatoshiLabs has done its utmost to assure the community that the fake devices are in no way identical to the original, and differ in both content and functioning capacity. The devices could also be spotted by their packaging, which include significant differences in the special holographic markings and the presence of ‘Made in China’ markings.
If you’re thinking about getting a hardware wallet then you should definitely watch this next video of a group of techies cracking a Trezor wallet. The security arms race favours hackers right now, but new hardware is being invented everyday.
Hot Wallets
A hot wallet is an online cryptocurrency storage device that maintains a constant connection to the internet. These commonly come in forms of apps for tablets and smartphones, but can also be connected to a computer.
Private keys generated by these wallets can never be considered 100% secure because they were generated on an internet connected device.
Pros of hot storage
- Quick to access funds.
- A wide number of options, and support for different devices.
- User-friendly user-interfaces simplify sending and receiving process.
Cons of hot storage
- Exposed to cybercrime. Sophisticated hackers, ransomware, and other malicious actors are a constant threat.
- Damaging the device could destroy the wallet. Without carefully backing up private keys, and seed words you could permanently lose your cryptocurrency investment.
- You could still lose/damage/have stolen the restoration details.
It’s best for folks who want a quick turnaround on their crypto-trading activity. Instead of getting out their Trezor wallet, satisfying its two-factor identification requirements, and uploading the key back onto the exchange to trade (which might jack you for a percentage of your stake just for showing up), these offer direct web-access through something as quick and accessible as an app on your phone.
The idea of attaching a cryptocurrency account to an application on a smartphone seems like an invitation to disaster, but it really depends on your comfort level and how well you assess and absorb certain risks.
If you’re going to store your cryptocurrency in a hot wallet, then there’s another term you’ll need to know: multisignature.
Multisignature (multisig) refers to requiring more than one key to authorize a Bitcoin transaction. It is generally used to divide up responsibility for possession of bitcoins. Most Bitcoin and altcoin transactions use a single signature key, which can be lost or stolen.
Here’s a video explaining how multisig technology works:
Web, mobile or desktop wallets:
BitGo supports multisig functionality and has been storing Bitcoin funds since 2013. It’s considered one of the most powerful Bitcoin wallets, and powers exchanges like ShapeShift, Bitstamp, BitBay, Bitfinex, Kraken and more. It allows the user to integrate their own multisig addresses with BitGo along with the Ledger Nano S and Ledger Blue – to alternate between hardware and hot wallets.
Services like this and Coinbase below put your Bitcoin private keys under their custody, and in that way are a lot more like banks than wallets, except without any accountability for when they get hacked. This isn’t a safe practice for obvious reasons.
BitGo has not been hacked yet, but BitFinex was using its software when it was hacked on August 2, 2016, and did process withdrawal requests from the hacker, who possessed BitFinex’s keys.
BitGo is available for Windows, Mac, Linux, Chrome Extension, iOS and Android.
Coinbase is one of the largest and well-known online bitcoin wallets in the world.
The site secures their digital currency through secure online servers and cold storage with a percentage ratio of 98% of their digital currency in cold storage with the remainder in secure online servers to cater to the liquidity needs of their customers.
Coinbase has not be hacked from the internet in that no-one has yet managed to penetrate their website, steal private keys through either a code-flaw, backdoor or brute-force attack, but the internet is absolutely full of Coinbase customers complaining about being hacked. The general gist is that if you can’t find a way through the core code into the website itself, then go to the end user.
One route through your e-mail, or access remote viewing on a different desktop computer and get any passwords stored on the computer. There’s a quick fix for this – don’t store any passwords or sensitive material related to your cryptocurrency on your computer.
The points of entry are legion.
Just as with cold storage wallets: the biggest, easiest and most plentiful hacks are the easiest to prevent as well.
Sometimes it’s just as simple as keeping your mouth shut.
Hodl strong until next week when we’ll close out crypto 101 with a discussion on how to pick the coin that’s right for you.
—Joseph Morton